Sha'carri Nude Updates For Private Content #856
Start Streaming sha'carri nude premier live feed. Completely free on our video archive. Engage with in a immense catalog of documentaries featured in unmatched quality, excellent for deluxe streaming gurus. With just-released media, you’ll always never miss a thing. Explore sha'carri nude selected streaming in high-fidelity visuals for a completely immersive journey. Join our media world today to get access to content you won't find anywhere else with for free, registration not required. Get fresh content often and journey through a landscape of bespoke user media designed for first-class media lovers. Be certain to experience distinctive content—get it fast! Witness the ultimate sha'carri nude exclusive user-generated videos with rich colors and staff picks.
Web self registration ussd self registration assisted enrolmentfrequently asked questions It takes an input message, such as a text, file, password, or any data input, and runs it through a mathematical process to generate a unique hash value known as a message digest or hash digest. They differ in the word size
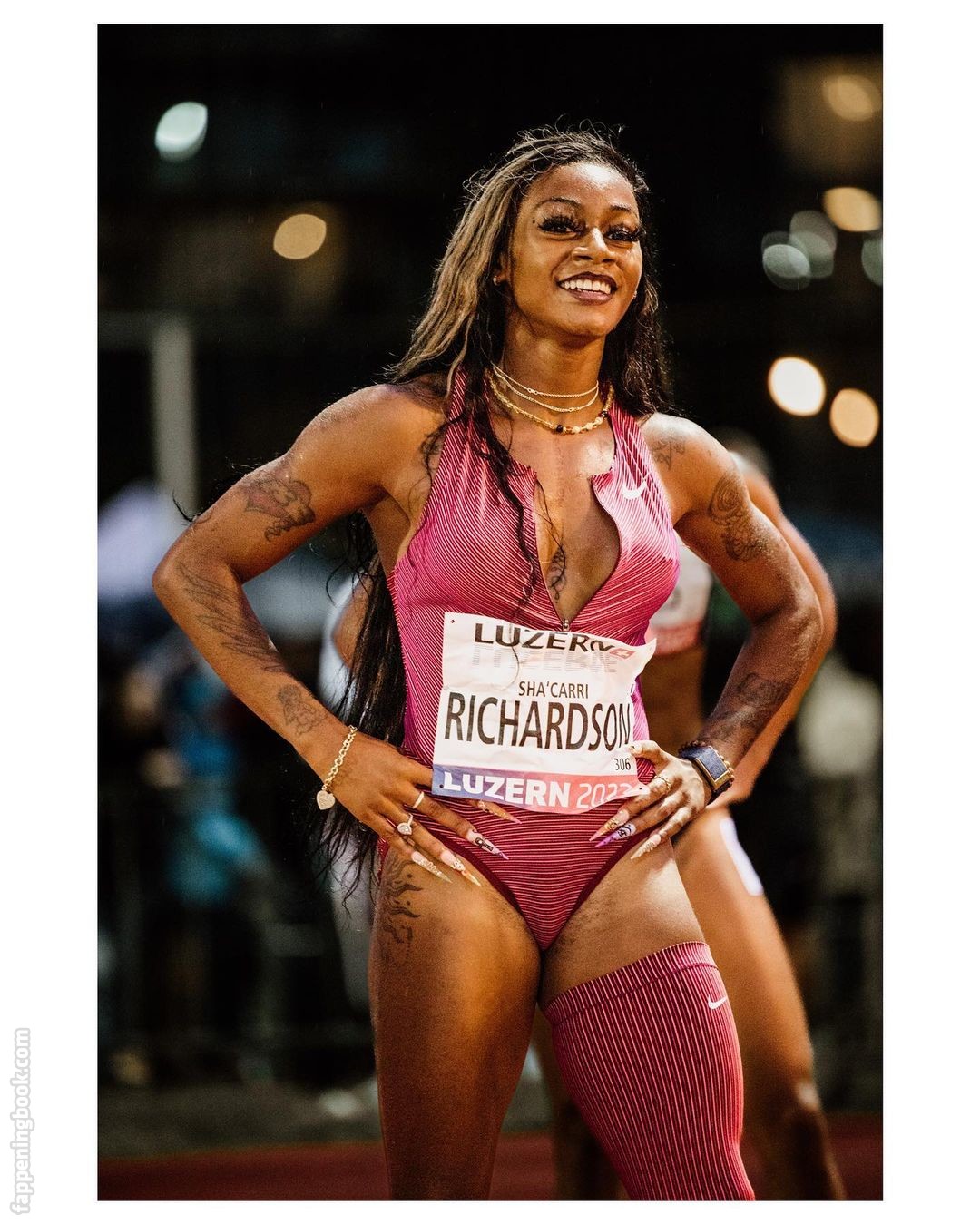
Sha'Carri Richardson aka carririchardson_ Nude Leaks - OnlyFans Leaked
A secure hashing algorithm, or sha, changes data by creating a hash digest unique to each plaintext message Sha stands for secure hash algorithm, a cryptographic function developed to protect sensitive data Sha is an acronym for secure hash algorithm, a family of cryptographic hash functions designed by the national security agency (nsa)
- Too Twisted Taboo Leaked Porn
- Sarah Cameron Sex
- Andy Cohen Nude Pictures
- Kevin Hart Sex Tape Leak
- Very Old Grandma Naked
This cryptographic hash function plays a critical role in ensuring the integrity and security of digital data.
Hashing is used for data integrity verification and to detect any unauthorized modification or tampering and can ensure the digital document's authenticity Secure hash algorithms (sha) is one of the cryptography technology and uses hashing for plaintext to message digest conversion. Secure hash algorithms, also known as sha, are a family of cryptographic functions designed to keep data secured It works by transforming the data using a hash function
An algorithm that consists of bitwise operations, modular additions, and compression functions.