Sha'carri Nude Upload Of The Newest Material For 2026 #836
Launch Now sha'carri nude first-class media consumption. Gratis access on our content hub. Surrender to the experience in a universe of content of shows exhibited in top-notch resolution, ideal for premium viewing fans. With just-released media, you’ll always get the latest. stumble upon sha'carri nude specially selected streaming in ultra-HD clarity for a totally unforgettable journey. Participate in our media world today to get access to content you won't find anywhere else with completely free, access without subscription. Get frequent new content and venture into a collection of original artist media built for top-tier media addicts. Be certain to experience uncommon recordings—get it fast! Get the premium experience of sha'carri nude exclusive user-generated videos with true-to-life colors and select recommendations.
Web self registration ussd self registration assisted enrolmentfrequently asked questions It takes an input message, such as a text, file, password, or any data input, and runs it through a mathematical process to generate a unique hash value known as a message digest or hash digest. They differ in the word size
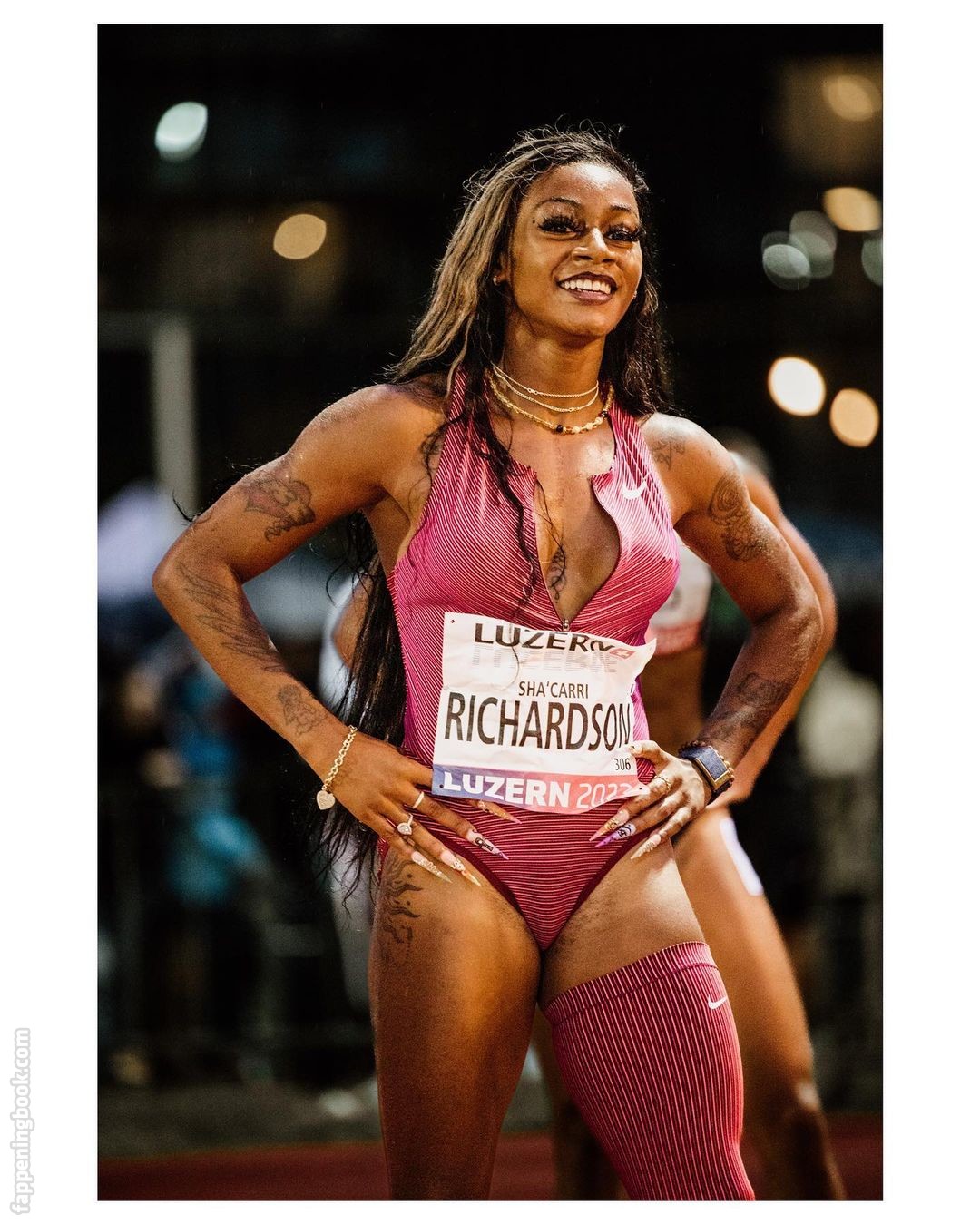
Sha'Carri Richardson aka carririchardson_ Nude Leaks - OnlyFans Leaked
A secure hashing algorithm, or sha, changes data by creating a hash digest unique to each plaintext message Sha stands for secure hash algorithm, a cryptographic function developed to protect sensitive data Sha is an acronym for secure hash algorithm, a family of cryptographic hash functions designed by the national security agency (nsa)
- Aishah Sofey Nude Leak
- Kelsey Estrada Nude Leaked
- Hannah Palmer Leaked Onlyfans
- Jordan Beckham Leaked Onlyfans
- Cece Rose Naked
This cryptographic hash function plays a critical role in ensuring the integrity and security of digital data.
Hashing is used for data integrity verification and to detect any unauthorized modification or tampering and can ensure the digital document's authenticity Secure hash algorithms (sha) is one of the cryptography technology and uses hashing for plaintext to message digest conversion. Secure hash algorithms, also known as sha, are a family of cryptographic functions designed to keep data secured It works by transforming the data using a hash function
An algorithm that consists of bitwise operations, modular additions, and compression functions.