Hackers Claim 64 Million T-mobile Customers' Data Leaked Update For New 2026 Files #718
Enter Now hackers claim 64 million t-mobile customers' data leaked boutique broadcast. Subscription-free on our media hub. Experience fully in a large database of videos exhibited in high definition, perfect for premium streaming geeks. With up-to-date media, you’ll always be ahead of the curve. Explore hackers claim 64 million t-mobile customers' data leaked curated streaming in life-like picture quality for a mind-blowing spectacle. Become a patron of our content portal today to enjoy exclusive prime videos with no charges involved, subscription not necessary. Receive consistent updates and investigate a universe of indie creator works conceptualized for deluxe media aficionados. Be sure not to miss unique videos—get a quick download! Witness the ultimate hackers claim 64 million t-mobile customers' data leaked one-of-a-kind creator videos with vivid imagery and members-only picks.
Hackers is a 1995 american crime thriller film directed by iain softley and starring jonny lee miller, angelina jolie, jesse bradford, matthew lillard, laurence mason, renoly santiago, lorraine bracco, and fisher stevens. A commonly used hacking definition is the act of compromising digital devices and networks through unauthorized access to an account or computer system. With jonny lee miller, angelina jolie, jesse bradford, matthew lillard
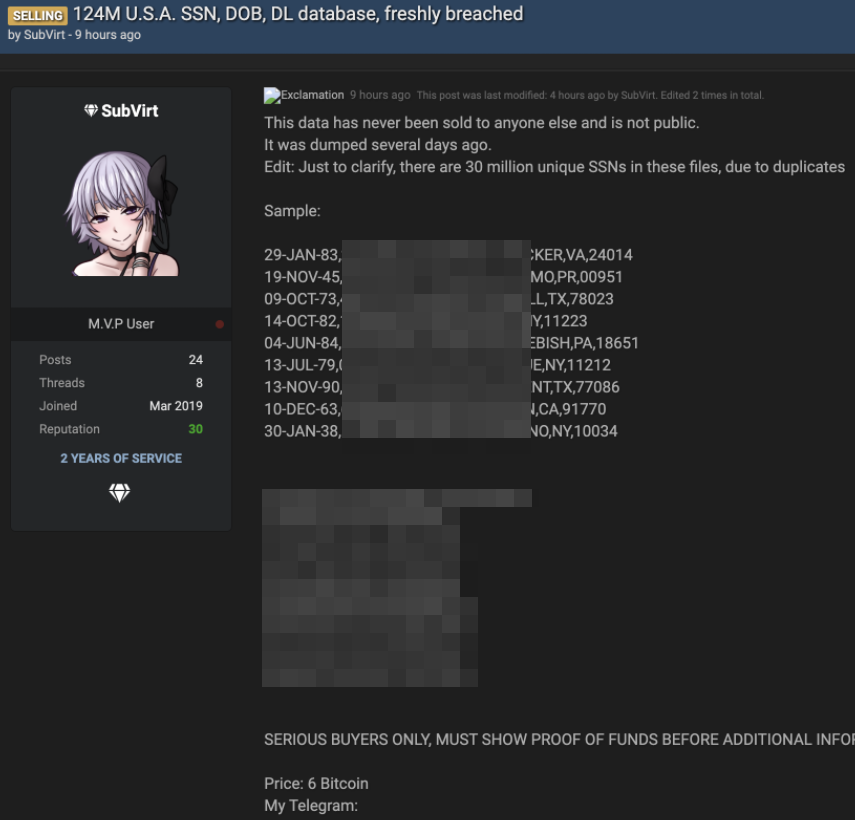
Hackers claim fresh T-Mobile data breach | Cybernews
Teenage hackers discover a criminal conspiracy with plans to use a computer virus that will capsize five oil tankers. Learn about the types of hackers, vulnerable devices to hacking, and hack prevention tips Hackers breach defenses to gain unauthorized access into computers, phones, tablets, iot devices, networks, or entire computing systems
- Poonam Pandey Leaked Video
- Too Twisted Taboo Leaked Porn
- Sexy Nudes On Beach
- Josie Bennett Onlyfans
- Selena Gomez Nude Photos Leaked
Hackers also take advantage of weaknesses in network security to gain access
The weaknesses can be technical or social in nature. White hat hackers play a crucial role in enhancing security by identifying and fixing vulnerabilities, while black hat hackers pose significant threats through malicious activities. Hackers break into computer systems, while refers to activities that seek to compromise digital devices, such as computers, smartphones, tablets, and even entire networks. A hacker is an individual who uses computer, networking or other skills to overcome a technical problem
The term also refers to anyone who uses such abilities to gain unauthorized access to systems or networks for illegal or unethical purposes. Hacker, information technology professionals or enthusiasts who compromise (or “hack”) the security of computers. Let’s break down 14 types of hackers you should know about — and whether they’re working for you or against you Hackers are individuals who use their technical knowledge to gain unauthorized access to systems, networks, or data.

Online scams now fund organized crime, hackers rent violence like a service, and even trusted apps or social platforms are turning into attack vectors
The result is a global system where every digital weakness can be turned into physical harm, economic loss, or political leverage.